Researchers at Sultan Qaboos University in Oman have developed an advanced intrusion detection system (IDS) that can identify cyber attacks with near-perfect accuracy while dramatically reducing processing time, according to a paper published in The Journal of Engineering Research (TJER).
The proposed system, which combines a double feature selection method with a stacked ensemble machine learning approach, achieved accuracy levels of up to 99.96 percent on benchmark datasets, with false alarm rates as low as 0.007 percent and detection times under 13 seconds.
As cyber threats targeting IoT devices, cloud computing infrastructure, and high-speed networks grow increasingly sophisticated, the research addresses critical vulnerabilities in existing detection methods that struggle with redundant feature processing, lengthy training periods, and imbalanced datasets.

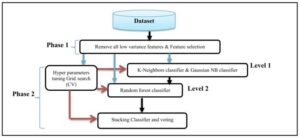
The system implements a two-phase feature reduction process designed to eliminate computational waste while preserving detection power. The Variance Threshold is first applied to remove low-variance features that contribute little to threat identification. This is followed by the Select-K-Best technique, which retains only the most relevant attributes for classification.
Through this rigorous filtration, the researchers successfully narrowed down datasets to as few as 13 or 19 significant features—a dramatic reduction that slashes processing time without compromising detection capability. This efficiency gain is critical for real-time cybersecurity applications where milliseconds matter.
At the heart of the system lies a stacking ensemble classification structure. Base learners consist of K-Nearest Neighbors and Gaussian Naive Bayes algorithms, which feed into a Random Forest classifier serving as the meta-classifier. The Random Forest model is optimized using Grid Search cross-validation to ensure peak performance.
This layered approach allows the system to leverage the strengths of multiple algorithms while compensating for individual weaknesses, resulting in more robust and reliable threat detection.
Rigorous Testing on Contemporary Threat Datasets
The model was validated using two benchmark datasets widely recognized in cybersecurity research: CIC-IDS2017 and CIC-DDoS2019. These datasets contain representations of current cyber attack types, including distributed denial-of-service (DDoS) attacks, denial-of-service (DoS) attacks, brute force attempts, port scans, web application attacks, and bot activity.
Experimental results demonstrated that the proposed system “outperforms various existing intrusion detection methods, effectively overcoming common shortcomings such as redundant feature processing, extended training times, and the challenges posed by imbalanced datasets where attack samples are significantly outnumbered by normal traffic.”
Real-World Applications
The authors emphasize that the method’s combination of efficient feature engineering and ensemble learning makes it suitable for practical, real-time cybersecurity deployments. As networks grow faster and more complex, the ability to detect threats quickly and accurately becomes increasingly critical for protecting infrastructure, data, and users.
Looking ahead, the researchers recommend “extending the approach to IoT environments, where resource constraints make lightweight yet accurate detection essential.” They also suggest integrating deep learning models with the current framework to further enhance detection capabilities against evolving threat landscapes.
The study adds to growing body of research exploring artificial intelligence applications in cybersecurity, a field racing to keep pace with increasingly sophisticated attack methods targeting everything from personal devices to critical national infrastructure.
Also Read:
As AI evolves, pressure mounts to regulate ‘killer robots
AI threatens one in four jobs – but transformation, not replacement, is the real risk

